I Analyzed Over 600 Real-World Ransomware Samples from the Wild – What They Actually Do Beyond File Encryption (Part 1)
 Modern ransomware is far more than just an encryptor — it’s a full-spectrum attack platform.
Modern ransomware is far more than just an encryptor — it’s a full-spectrum attack platform.
Author: Aayush Pantha@lucy01 Role: Cybersecurity Researcher & Red Team Operator
Date: March 2026
Executive Summary
Between January and February 2026, I conducted an intensive analysis of more than 600 live ransomware samples belonging to over 100 distinct families. The goal was simple yet brutal: test the real-world effectiveness of a commercial endpoint protection platform (EPP/EDR) by executing samples in controlled environments and observing every stage of the attack chain.
What I discovered goes far beyond the classic “encrypt files → drop ransom note” narrative that most defenders still focus on. Modern ransomware operates as a multi-stage, multi-purpose malware platform that combines data theft, anti-analysis, system sabotage, persistence, and psychological operations — all before a single file is encrypted.
This is Part 1 of a two-part series. Here I detail the unexpected behaviors I observed across the dataset. Part 2 will cover how I built my own custom ransomware and successfully evaded multiple commercial security products.
Research Methodology & Dataset
- Volume: 600+ unique samples
- Families covered (partial list): LockBit (3.0 & 4.0), Akira, Cl0p, REvil (Sodinokibi), Conti, Ryuk, BlackBasta, BlackMatter, DarkSide, Maze, Hive, Medusa, BianLian, Qilin, Rhysida, Avaddon, Nefilim, Pysa/Mespinoza, HelloKitty (Vice Society overlap), Trigona, RA World (formerly RA Group), BlackCat (ALPHV), Ragnar Locker, and dozens more.
- Average samples per family: 10
- Sources: ANY.RUN threat intelligence platform, MalwareBazaar, VX-Underground archive, public GitHub repositories, and limited private feeds.
- Analysis environment: Physical hardware + isolated virtual machines. Cloud-based sandboxes were deliberately avoided after early failures.
- Testing objective: Execute samples and record every pre-encryption, encryption, and post-encryption behavior while monitoring EPP/EDR telemetry.
All samples were detonated in a controlled lab with proper containment. No production systems were harmed.
 Physical bare-metal lab used for safe detonation of 600+ samples
Physical bare-metal lab used for safe detonation of 600+ samples
1. Anti-Analysis & Environment Awareness (They Know You’re Watching)
A surprising number of families include sophisticated checks to detect virtual machines, sandboxes, or cloud instances.
Key findings:
- BlackCat (ALPHV) and Ragnar Locker were the most aggressive against VirtualBox. They inspected registry keys (e.g.,
HKLM\SOFTWARE\Oracle\VirtualBox Guest Additions), running processes (vboxsvc.exe,VBoxTray.exe), MAC address OUIs, CPUID leaf values, and hardware artifacts. - Four samples specifically detected cloud environments (AWS, Azure, GCP). Detection methods included querying instance metadata endpoints (
169.254.169.254) and checking for cloud-specific drivers or processes. - Behavior on detection: These samples refused to execute entirely no encryption, no ransom note, no artifacts left behind. I had to migrate analysis to bare-metal physical desktops to continue.
Defender takeaway: If your sandbox or analysis environment is cloud-hosted or uses common VM fingerprints, you are effectively blind to a non-trivial percentage of modern ransomware.
2. Espionage & Data Exfiltration (Spyware First, Encryption Second)
Almost every major family now includes a full stealer component before encryption begins.
Observed capabilities:
- Dumping the SAM/SYSTEM/SECURITY registry hives for local account credentials
- Harvesting browser-stored passwords (Chrome, Edge, Firefox) via DPAPI or direct SQLite extraction
- Capturing desktop screenshots (including wallpaper for victim identification/proof)
- Installing a keylogger to capture typed credentials in real time
- Exfiltrating all stolen data via Telegram bots (the most common channel) or custom C2 infrastructure
Exfiltration happened quietly and often in parallel with other activities. Several samples waited for user interaction (mouse/keyboard activity) before sending data, reducing the chance of detection during idle sandbox runs.
Why this matters: This is classic double (or triple) extortion — steal data → threaten to leak → encrypt → demand payment. Defenders who only watch for file-encryption patterns miss the entire first half of the attack.
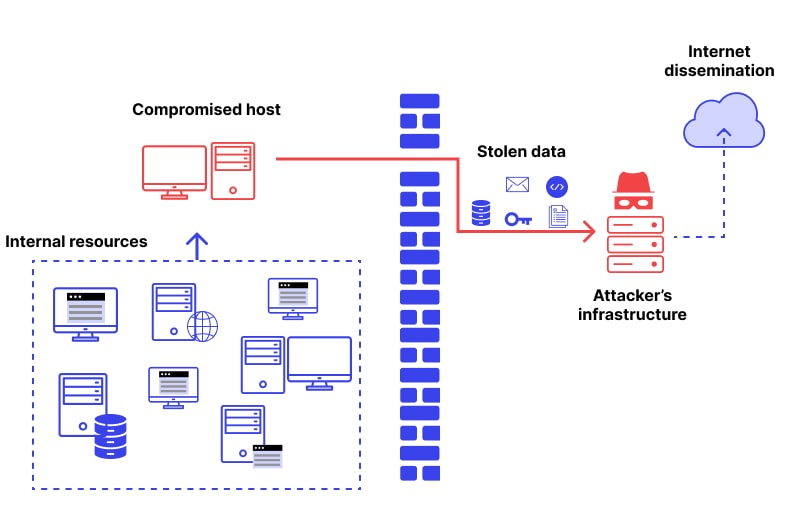 Typical pre-encryption espionage pipeline (credentials → screenshots → Telegram C2)
Typical pre-encryption espionage pipeline (credentials → screenshots → Telegram C2)
3. Screen Hijacking & Psychological Operations
Several families went beyond encryption and took complete control of the user experience.
Observed techniques:
- Full-screen black overlay with embedded ransom wallet address
- Playback of meme videos or looping corrupt-disk sounds (the classic grinding HDD failure noise) over the ransom screen
- Complete disabling of user interaction — nothing clickable, Explorer.exe killed or hooked, desktop frozen
- Targeted interference with File Explorer and Notepad (preventing opening or viewing of any text files)
Families most aggressive here: Medusa and RA World stood out.
One sample (Medusa lineage) went even further by modifying the Windows Boot Configuration Data (BCD) via bcdedit commands — disabling Safe Mode, recovery options, and shadow copy services. The result? The machine became unbootable after encryption, forcing a complete OS reinstall. I personally had to wipe and reinstall the test system.
This isn’t just ransomware. This is digital terrorism designed to maximize panic and pressure.
 Full-screen psychological warfare overlay used by aggressive families (Medusa)
Full-screen psychological warfare overlay used by aggressive families (Medusa)
4. Self-Replication, Persistence & Dropper Tactics
Multiple families employed advanced dropper and anti-forensic techniques:
- Self-replacing binaries: Drop a new executable in a different location → delete the original → execute the new copy (observed in several multistage families, especially RA World).
- Creation of multiple identical copies across system directories to survive partial detection.
- VM/cloud re-checking even after initial execution.
- Modification of system components (wallpaper changes, registry persistence, service creation).
These tactics dramatically increase the difficulty of both automated detection and manual cleanup.
5. The Single Biggest Lesson After 600 Samples
Ransomware in 2026 is no longer a simple encryptor.
“Ransomware doesn’t only encrypt files, it corrupts bootloaders, creates file copies for persistence, communicates with C2 servers, implants keystroke loggers, changes wallpapers, steals credentials, hijacks the entire screen, and deploys psychological warfare tactics.”
The encryption step is now just the final visible stage of a much larger, multi-purpose infection chain.
Most organizations and even many security products still focus almost exclusively on file-encryption signatures and ransom-note detection. That approach is dangerously outdated.
Coming in Part 2
I will walk through the custom ransomware I developed during this research, including the exact evasion techniques that successfully bypassed multiple commercial EDR/AV/XDR solutions — and what real-world lessons I learned about modern detection gaps.
Connect me on:
Linkedin: https://www.linkedin.com/in/aayushpantha/
Twitter: https://x.com/aayushpantha01
Medium: https://medium.com/@aayushpantha
Stay tuned.
#Ransomware #Cybersecurity #MalwareAnalysis #RedTeaming #EndpointSecurity